[ad_1] More than five years after domain name registrars started redacting personal data from all public domain registration records, the
[ad_1] Dec 06, 2023NewsroomAccess Management / Cloud Security Threat actors can take advantage of Amazon Web Services Security Token Service
[ad_1] Dec 06, 2023NewsroomCyber Threat / Vulnerability A collection of 21 security flaws have been discovered in Sierra Wireless AirLink
[ad_1] Dec 06, 2023The Hacker NewsBrowser Security / Privacy Compromising the browser is a high-return target for adversaries. Browser extensions,
[ad_1] Dec 06, 2023NewsroomSoftware Security / Vulnerability Atlassian has released software fixes to address four critical flaws in its software
[ad_1] Dec 06, 2023NewsroomVulnerability / Mobile Security Chipmaker Qualcomm has released more information about three high-severity security flaws that it
[ad_1] Dec 05, 2023NewsroomMobile Security / Spyware A new “post-exploitation tampering technique” can be abused by malicious actors to visually
[ad_1] Dec 05, 2023NewsroomBrandjacking / Artificial Intelligence The Russia-linked influence operation called Doppelganger has targeted Ukrainian, U.S., and German audiences
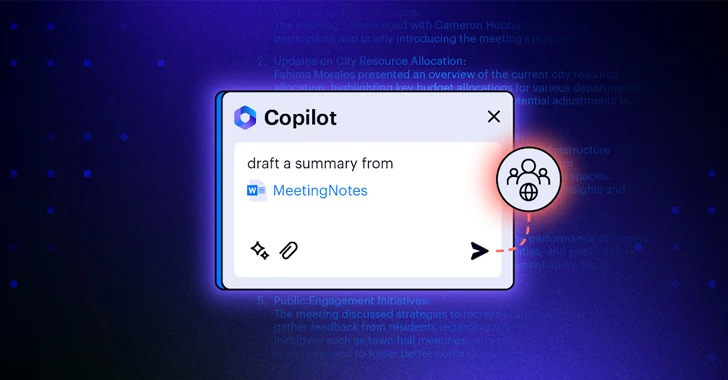
[ad_1] Microsoft Copilot has been called one of the most powerful productivity tools on the planet. Copilot is an AI
[ad_1] Dec 05, 2023NewsroomSoftware Security / Supply Chain New research has found that over 15,000 Go module repositories on GitHub