[ad_1] The Hacker NewsMar 05, 2026Encryption / Data Protection Most organizations assume encrypted data is safe. But many attackers are
[ad_1] Ravie LakshmananMar 05, 2026Cybersecurity / Hacking News Some weeks in cybersecurity feel routine. This one doesn’t. Several new developments
[ad_1] Ravie LakshmananMar 05, 2026Malware / Threat Intelligence A suspected Iran-nexus threat actor has been attributed to a campaign targeting
[ad_1] Organizations typically roll out multi-factor authentication (MFA) and assume stolen passwords are no longer enough to access systems. In
[ad_1] Ravie LakshmananMar 05, 2026Cyber Espionage / Threat Intelligence Cybersecurity researchers have disclosed details of a new Russian cyber campaign
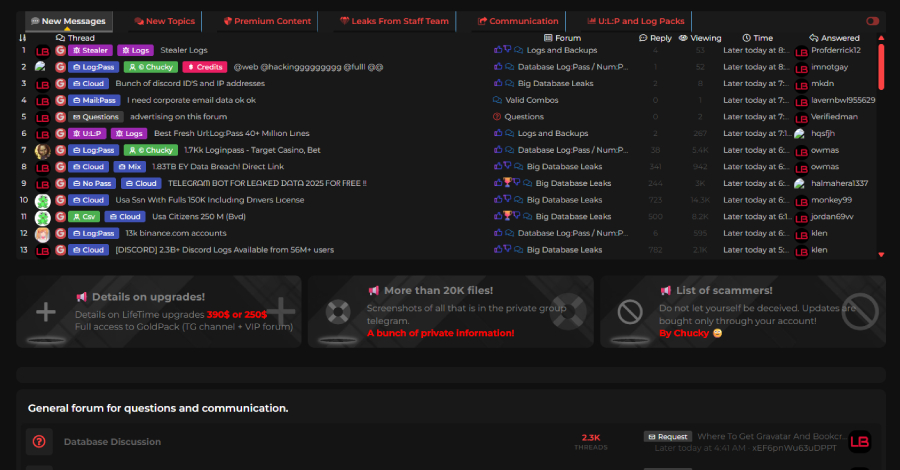
[ad_1] Ravie LakshmananMar 05, 2026Malware / Dark Web A joint law enforcement operation has dismantled LeakBase, one of the world’s
[ad_1] Tycoon 2FA, one of the prominent phishing-as-a-service (PhaaS) toolkits that allowed cybercriminals to stage adversary-in-the-middle (AitM) credential harvesting attacks
[ad_1] Cybersecurity researchers have warned of a surge in retaliatory hacktivist activity following the U.S.-Israel coordinated military campaign against Iran,
[ad_1] Google said it identified a “new and powerful” exploit kit dubbed Coruna (aka CryptoWaters) targeting Apple iPhone models running
[ad_1] The Hacker NewsMar 04, 2026Artificial Intelligence / SaaS Security As AI becomes the central engine for enterprise productivity, security