[ad_1] When a Magecart payload hides inside the EXIF data of a dynamically loaded third-party favicon, no repository scanner will
[ad_1] Security teams today are not short on tools or data. They are overwhelmed by both. Yet within the terabytes
[ad_1] Ravie LakshmananMar 18, 2026Linux / Endpoint Security A high-severity security flaw affecting default installations of Ubuntu Desktop versions 24.04
[ad_1] Ravie LakshmananMar 18, 2026Vulnerability / Zero-Day Apple on Tuesday released its first round of Background Security Improvements to address
[ad_1] Ravie LakshmananMar 18, 2026Vulnerability / Data Protection Cybersecurity researchers have disclosed a critical security flaw impacting the GNU InetUtils
[ad_1] Cybersecurity researchers have disclosed details of a new method for exfiltrating sensitive data from artificial intelligence (AI) code execution
[ad_1] The ransomware operation known as LeakNet has adopted the ClickFix social engineering tactic delivered through compromised websites as an
[ad_1] The Hacker NewsMar 17, 2026Artificial Intelligence / Security Leadership A majority of security leaders are struggling to defend AI
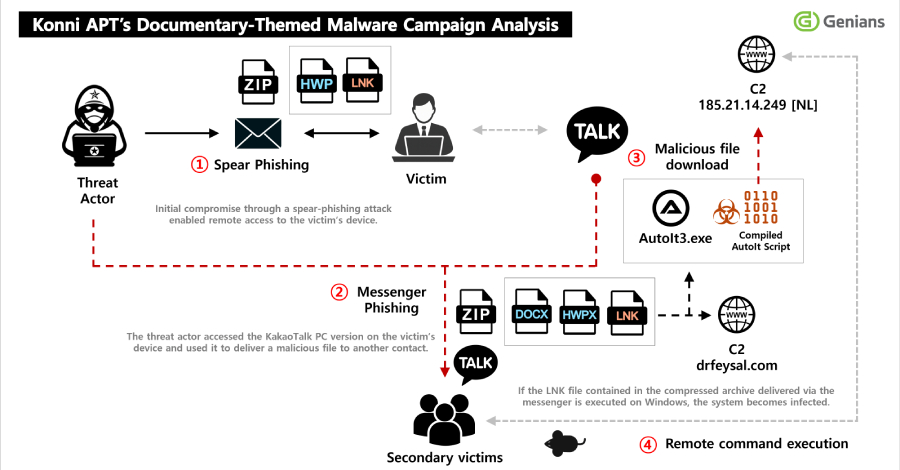
[ad_1] Ravie LakshmananMar 17, 2026Threat Intelligence / Endpoint Security North Korean threat actors have been observed sending phishing to compromise
[ad_1] Ravie LakshmananMar 17, 2026Vulnerability / Network Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a